A Quiet Evening Turned Chaotic
It was a chilly evening on November 2, 1988. The internet, a burgeoning network primarily used by academics and researchers, hummed smoothly. At Cornell University, a young graduate student named Robert Tappan Morris was about to conduct an experiment that would inadvertently send shockwaves through the digital world.
Robert Tappan Morris, a graduate student at Cornell University, was fueled by a deep curiosity about the nascent internet. At the time, the internet was a much smaller and less understood entity, primarily connecting academic and research institutions. Morris was intrigued by a fundamental question: how large was the internet? To answer this, he decided to create a self-replicating program that could traverse the network, copy itself to other computers, and report back, giving an indication of the internet’s scale.
This program, which he named the Morris Worm, was carefully crafted to spread autonomously from one computer to another. It was designed to exploit several known vulnerabilities in Unix-based systems, which were the predominant operating systems used by computers connected to the internet. One of these vulnerabilities was in the sendmail program, a widely used mail transfer agent that had a debug mode Morris’s worm could exploit to gain unauthorized access to the system. Another target was the fingerd service, which provided user information and had a buffer overflow vulnerability the worm could exploit to inject its code.
In addition to these vulnerabilities, the Morris Worm also leveraged weak password security. It included a dictionary of commonly used passwords and attempted to gain access by guessing user passwords. Once the worm successfully infiltrated a system, it used the system’s resources to continue replicating and sending copies of itself to other computers.
Morris’s intention was not to cause harm but to measure the reach and size of the internet. However, his program included a critical flaw: it was overly aggressive in its replication strategy. Morris had included a feature to prevent multiple copies of the worm from running on a single machine, but this feature was not foolproof. As a result, the worm replicated excessively, even on systems it had already infected.
As soon as the worm was released, it began to spread rapidly, moving from one vulnerable system to another. The worm’s aggressive replication and resource consumption caused significant disruption. Systems were overwhelmed by the numerous copies of the worm, which led to severe slowdowns and, in many cases, rendered the machines unusable. What began as an academic experiment to map the internet’s size quickly spiralled out of control, becoming one of the first major cybersecurity incidents and highlighting the internet’s vulnerabilities.
The Chaos Unfolds
Within hours, the worm had spread like wildfire, infecting thousands of computers across the United States. These infected machines represented about 10% of the internet at the time. Network administrators were caught off guard as their systems, which had previously run smoothly, ground to a halt. The worm’s rapid replication consumed system resources, leading to severe slowdowns and making many machines inoperable.
Panic ensued. University IT departments were inundated with calls. “My computer is acting strange,” one user would report. Another would exclaim, “I can’t get any work done!” As administrators scrambled to understand and contain the outbreak, the term “computer worm” quickly became a part of their vocabulary.
A Call for Help
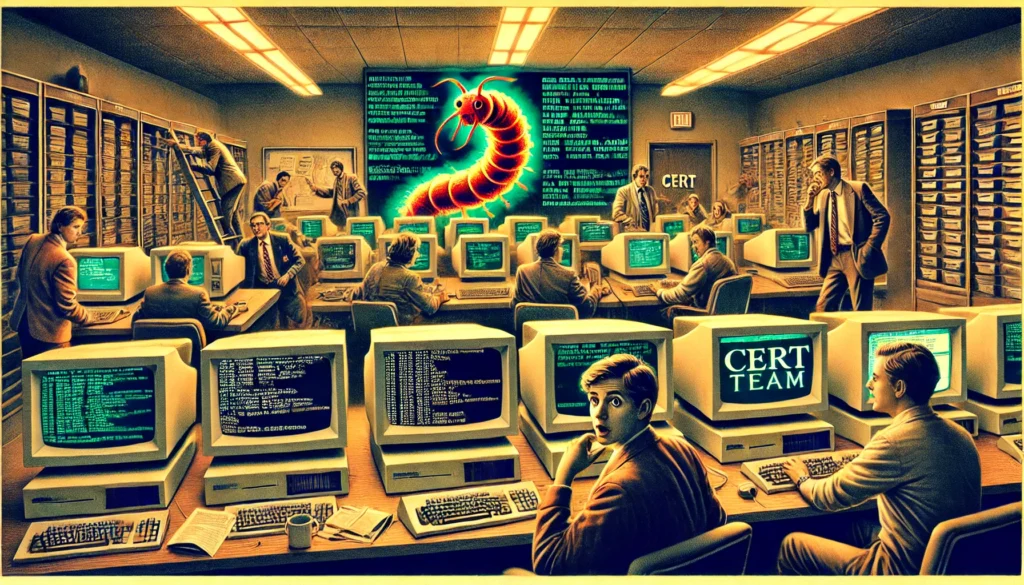
The widespread disruption caused by the Morris Worm highlighted a significant vulnerability in the burgeoning digital landscape. DARPA, the Defense Advanced Research Projects Agency, recognized the severity of the threat and the need for a coordinated response. This realization led to the formation of the Computer Emergency Response Team (CERT).
DARPA funded the establishment of CERT/CC (Coordination Center) at Carnegie Mellon University’s Software Engineering Institute (SEI). This team of cybersecurity pioneers was tasked with responding to security incidents, analyzing vulnerabilities, and disseminating critical information to prevent future attacks.
The Birth of CERT
CERT/CC’s creation marked a turning point in the field of cybersecurity. The team’s mission was clear: provide a rapid response to computer security incidents, offer assistance to affected organizations, and educate the public on best practices for computer security. Their efforts were instrumental in containing the Morris Worm and mitigating its impact.
CERT/CC quickly became a vital resource for network administrators and cybersecurity professionals. They issued advisories, developed patches, and coordinated responses to help organizations recover from the worm’s damage. This incident underscored the need for proactive measures and continuous vigilance in the face of evolving cyber threats.
The Legacy
The Morris Worm incident and the subsequent formation of CERT were pivotal moments in the history of cybersecurity. They highlighted the vulnerabilities inherent in interconnected systems and demonstrated the potential for widespread disruption from a single malicious program. More importantly, they emphasized the necessity for coordinated response efforts and proactive security measures.
The establishment of CERT/CC laid the foundation for modern cybersecurity practices. Today, a global network of Computer Security Incident Response Teams (CSIRTs) works tirelessly to address cybersecurity threats. These teams collaborate, share information, and develop strategies to protect against ever-evolving cyber threats.
The Morris Worm served as a wake-up call, prompting a shift in how we approach cybersecurity. It highlighted the importance of preparedness, research, and education. The lessons learned from this incident continue to guide our efforts to secure the digital world.
This narrative, though rooted in the past, is more relevant than ever. As we face new and complex cyber threats, the pioneering efforts of CERT/CC serve as a beacon, guiding our path forward. The Morris Worm incident taught us that cybersecurity is not just a technical challenge but a continuous journey of vigilance and adaptation.